In an interview, Marc Lynch discusses his new book decrying the post-1990 U.S.-dominated order in the Middle East.
Michael Young
{
"authors": [
"Tim Maurer"
],
"type": "other",
"centerAffiliationAll": "dc",
"centers": [
"Carnegie Endowment for International Peace"
],
"collections": [
"Cyber and Digital Policy"
],
"englishNewsletterAll": "ctw",
"nonEnglishNewsletterAll": "",
"primaryCenter": "Carnegie Endowment for International Peace",
"programAffiliation": "NPP",
"programs": [
"Nuclear Policy",
"Technology and International Affairs"
],
"projects": [],
"regions": [
"Iran"
],
"topics": [
"Foreign Policy",
"Technology"
]
}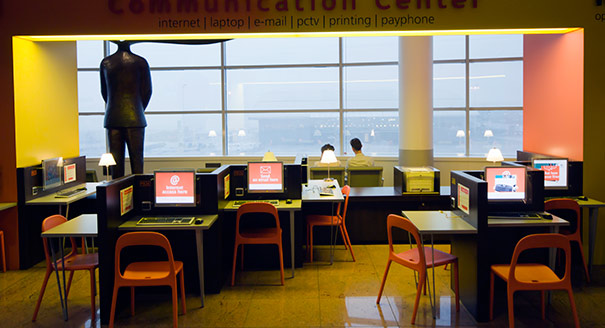
Source: Getty
States use proxies to project power through cyberspace, some capable of causing significant harm. But there is a lack of clarity on what, exactly, the term ‘proxy’ means.
Source: Journal of Conflict and Security Law
States use proxies to project power through cyberspace, some capable of causing significant harm. In recent years, media outlets have published reports about proxies using Information and Communications Technologies (ICTs) from Northeast Asia to India, Pakistan, the Middle East, and Eastern Europe. Two of the landmark documents providing insight into how the international community thinks about rules of the road for cyberspace explicitly reference the term ‘proxies’. However, neither report defines ‘proxy’, nor does the term easily translate into non-English languages. This article therefore reviews what this term means and how it has been used in various contexts. It focuses on the subset of proxies that are non-state actors used by a state actor, analysing the different logical distinctions and levels of detachment between a state and a non-state actor’s activity. The goal is 2-fold: first, to provide a framework to think about the diverse array of existing proxy definitions; second, to conceptualise the relationships between a state and non-state proxies that can offer a guide for political decision-makers and a roadmap for future research on proxy actors and cyberspace.
This article was originally published in the Journal of Conflict and Security Law.

Tim Maurer
Former Senior Fellow, Technology and International Affairs Program
Dr. Tim Maurer was a senior fellow in Carnegie’s Technology and International Affairs program.
Carnegie does not take institutional positions on public policy issues; the views represented herein are those of the author(s) and do not necessarily reflect the views of Carnegie, its staff, or its trustees.
In an interview, Marc Lynch discusses his new book decrying the post-1990 U.S.-dominated order in the Middle East.

Michael Young
Because perpetual conflict enhances control, offers economic benefits, and allows leaders to ignore popular preferences.

Angie Omar
In an interview, Jim Lamson discusses the ongoing regional conflict and sees an unclear picture when it comes to winners and losers.

Michael Young
Cairo’s efforts send a message to the United States and the region that it still has a place at the diplomatic table.

Angie Omar
Beirut’s desire to break free from Iranian hegemony may push it into a situation where it has to accept Israel’s hegemony.

Michael Young