Katherine Charlet, Danielle Citron
{
"authors": [
"Katherine Charlet"
],
"type": "legacyinthemedia",
"centerAffiliationAll": "dc",
"centers": [
"Carnegie Endowment for International Peace"
],
"collections": [],
"englishNewsletterAll": "ctw",
"nonEnglishNewsletterAll": "",
"primaryCenter": "Carnegie Endowment for International Peace",
"programAffiliation": "TIA",
"programs": [
"Technology and International Affairs"
],
"projects": [],
"regions": [
"North America",
"United States",
"Russia",
"Iran"
],
"topics": [
"Security",
"Foreign Policy",
"Technology"
]
}
Source: Getty
Sanctions Announcement Reveals Hacks of U.S. Critical Infrastructure
One genuine piece of news behind the U.S. sanctions against Russian individuals and organizations is the attribution to Russia of a hacking campaign that has targeted critical U.S. infrastructure.
Source: Axios
One genuine piece of news behind the U.S. sanctions against Russian individuals and organizations is the attribution to Russia of a cyberhacking campaign that has targeted critical U.S. infrastructure.
The details: Per the Treasury Department’s statement, “Since at least March 2016, Russian government cyber actors have also targeted … the energy, nuclear, commercial facilities, water, aviation and critical manufacturing sectors.”
The Department of Homeland Security has previously reported on cyber intrusions into critical infrastructure but has only identified an “Advanced Persistent Threat” without pointing the finger at a suspected culprit. In a move surely coordinated with Treasury’s announcement, the DHS updated its alert to note the Russian attribution and describe a “multi-stage campaign” into energy sector networks that included collection of “information pertaining to Industrial Control Systems.”
Why it matters: This attribution reinforces the need to secure critical infrastructure and continues a series of actions that have picked up steam since Homeland Security Advisor Tom Bossert told an audience last June that the U.S. government would “call out bad behavior and impose costs on our adversaries.” These include removal of Kaspersky from U.S. government systems, special counsel indictments,naming-and-shaming of Russia for the NotPetya attacks and this week’s sanctions and attribution.
What's next: These moves aren’t yet enough to stop Russia’s bad behavior. But it’s hard to imagine matters ending here.
About the Author
Former Director, Technology and International Affairs Program
Katherine Charlet was the inaugural director of Carnegie’s Technology and International Affairs Program.
- Campaigns Must Prepare for Deepfakes: This Is What Their Plan Should Look LikeCommentary
- What the Machine Learning Value Chain Means for GeopoliticsArticle
- +3
Charlotte Stanton, Vivien Lung, Nancy (Hanzhuo) Zhang, …
Recent Work
Carnegie does not take institutional positions on public policy issues; the views represented herein are those of the author(s) and do not necessarily reflect the views of Carnegie, its staff, or its trustees.
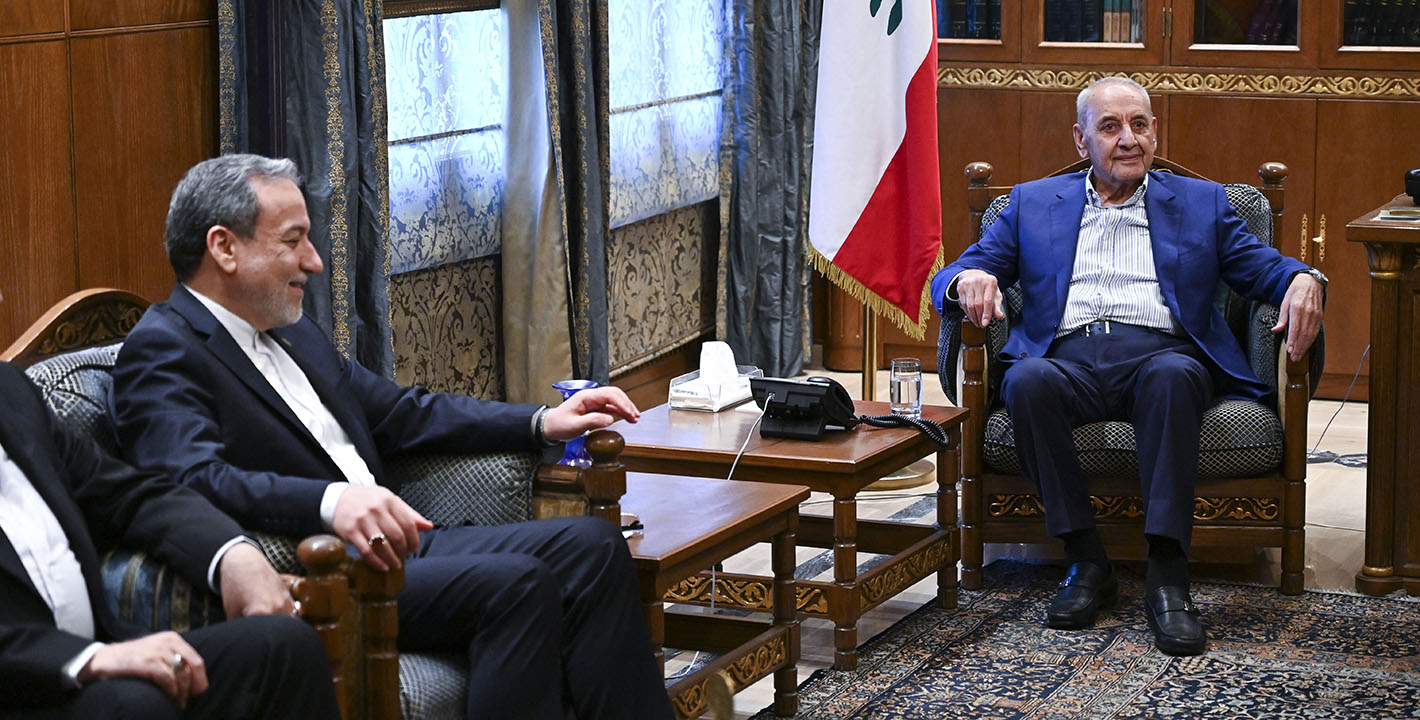
More Work from Malcolm H. Kerr Carnegie Middle East Center
- Pushing Beirut into an Armed Conflict With Hezbollah Is InsaneCommentary
The party’s domestic and regional roles have changed, so Lebanon should devise a disarmament strategy that encompasses this.
Michael Young
- Corrupted by Absolute PowerCommentary
In an interview, Marc Lynch discusses his new book decrying the post-1990 U.S.-dominated order in the Middle East.
Michael Young
- Why Does the Middle East Suffer “Forever Wars”?Commentary
Because perpetual conflict enhances control, offers economic benefits, and allows leaders to ignore popular preferences.
Angie Omar
- Where is the Groundwork for Lebanon’s Negotiations With Israel?Commentary
A prerequisite of serious talks is that the country’s leadership consolidates majority national support for such a process.
Michael Young
- A Military Balance Sheet in the U.S. and Israeli War With IranCommentary
In an interview, Jim Lamson discusses the ongoing regional conflict and sees an unclear picture when it comes to winners and losers.
Michael Young