- +18
James M. Acton, Saskia Brechenmacher, Cecily Brewer, …
{
"authors": [
"James M. Acton"
],
"type": "other",
"centerAffiliationAll": "dc",
"centers": [
"Carnegie Endowment for International Peace"
],
"collections": [],
"englishNewsletterAll": "ctw",
"nonEnglishNewsletterAll": "",
"primaryCenter": "Carnegie Endowment for International Peace",
"programAffiliation": "NPP",
"programs": [
"Nuclear Policy"
],
"projects": [],
"regions": [],
"topics": [
"Nuclear Policy",
"Foreign Policy"
]
}
Source: Getty
Cyber Warfare and Inadvertent Escalation
The advent of cyber warfare exacerbates the risk that conventional wars could inadvertently lead to the use of nuclear weapons.
Source: Daedalus
Cyber weapons may be relatively new, but non-nuclear threats to nuclear weapons and their command, control, communication, and intelligence (C3I) systems are not. In fact, before the United States dropped the bomb on Hiroshima in August 1945–before it even conducted the world’s first nuclear test in July of that year–it had started to worry about non-nuclear threats to its nascent nuclear force, in particular, Japanese air defenses. As the Cold War developed, fears multiplied to encompass threats to almost every component of the United States’ nuclear forces and C3I systems. While these threats emanated primarily from Moscow’s nuclear forces, they were exacerbated by its improving non-nuclear capabilities, particularly in the final decade of the Cold War. A two-decade hiatus in worry following the Soviet Union’s collapse is now over; today, non-nuclear threats to U.S. nuclear C3I assets–in particular, the growing capability of Chinese and Russian antisatellite weapons–are a major concern.
The United States’ experience is the norm. All nuclear-armed states have felt, and continue to feel, similar concerns. Indeed, the last few decades have seen the emergence of new potential vulnerabilities–this time in cyberspace–as nuclear weapons and C3I systems have come to rely increasingly on digital technology. To be sure, the networks involved in nuclear operations are almost certainly among the most secure anywhere. Yet there is broad agreement among technical experts that perfect network security is “impossible.” As a result, the possibility of cyber interference with nuclear forces and C3I systems is real.
The full article is published in the Spring 2020 issue of Daedalus.
About the Author

Jessica T. Mathews Chair, Co-director, Nuclear Policy Program
Acton holds the Jessica T. Mathews Chair and is co-director of the Nuclear Policy Program at the Carnegie Endowment for International Peace.
- Unpacking Trump’s National Security StrategyOther
- Trump Has an Out on Nuclear Testing. He Should Take It.Commentary
James M. Acton
Recent Work
Carnegie does not take institutional positions on public policy issues; the views represented herein are those of the author(s) and do not necessarily reflect the views of Carnegie, its staff, or its trustees.
More Work from Carnegie China
- Trump and Xi Are Angling for Three Years of StabilityCommentary
But their "principal to principal" model will only be as effective as the political strength of each leader back home.
Damien Ma
- China Sells Stability Amid American VolatilityCommentary
U.S. unpredictability has allowed China to capitalize on its positioning as the “responsible great power”. Paradoxically, the more China wins the perception game, the more likely expectations will rise for Beijing to deliver not just words but to demonstrate with its deeds.
Chong Ja Ian
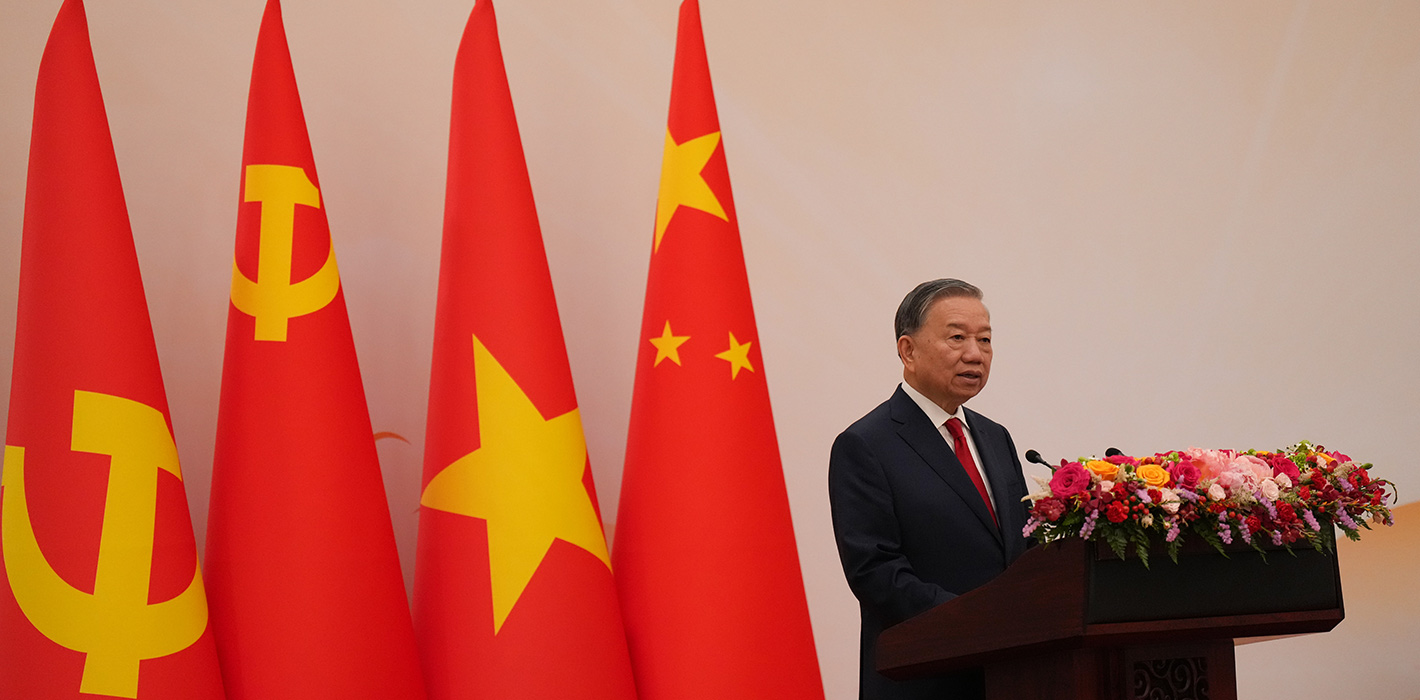
- Why Vietnam Is Swinging in China’s DirectionCommentary
Hanoi and Beijing have long treated each other as distant cousins rather than comrades in arms. That might be changing as both sides draw closer to hedge against uncertainty and America’s erratic behavior.
Nguyễn Khắc Giang
- China’s Energy Security Doesn’t Run Through Hormuz but Through the Electrification of EverythingCommentary
Across Asia, China is better positioned to withstand energy shocks from the fallout of the Iran war. Its abundant coal capacity can ensure stability in the near term. Yet at the same time, the country’s energy transition away from coal will make it even less vulnerable during the next shock.
Damien Ma
- Malaysia’s Year as ASEAN Chair: Managing DisorderCommentary
Malaysia’s chairmanship sought to fend off short-term challenges while laying the groundwork for minimizing ASEAN’s longer-term exposure to external stresses.
Elina Noor