Jon Bateman, Nick Beecroft, Gavin Wilde
{
"authors": [
"Nick Beecroft"
],
"type": "commentary",
"centerAffiliationAll": "dc",
"centers": [
"Carnegie Endowment for International Peace"
],
"collections": [
"Ukraine’s Long Shadow"
],
"englishNewsletterAll": "ctw",
"nonEnglishNewsletterAll": "",
"primaryCenter": "Carnegie Endowment for International Peace",
"programAffiliation": "TIA",
"programs": [
"Technology and International Affairs"
],
"projects": [],
"regions": [
"Russia",
"Eastern Europe",
"Ukraine",
"Iran"
],
"topics": [
"Security",
"Foreign Policy",
"Technology"
]
}
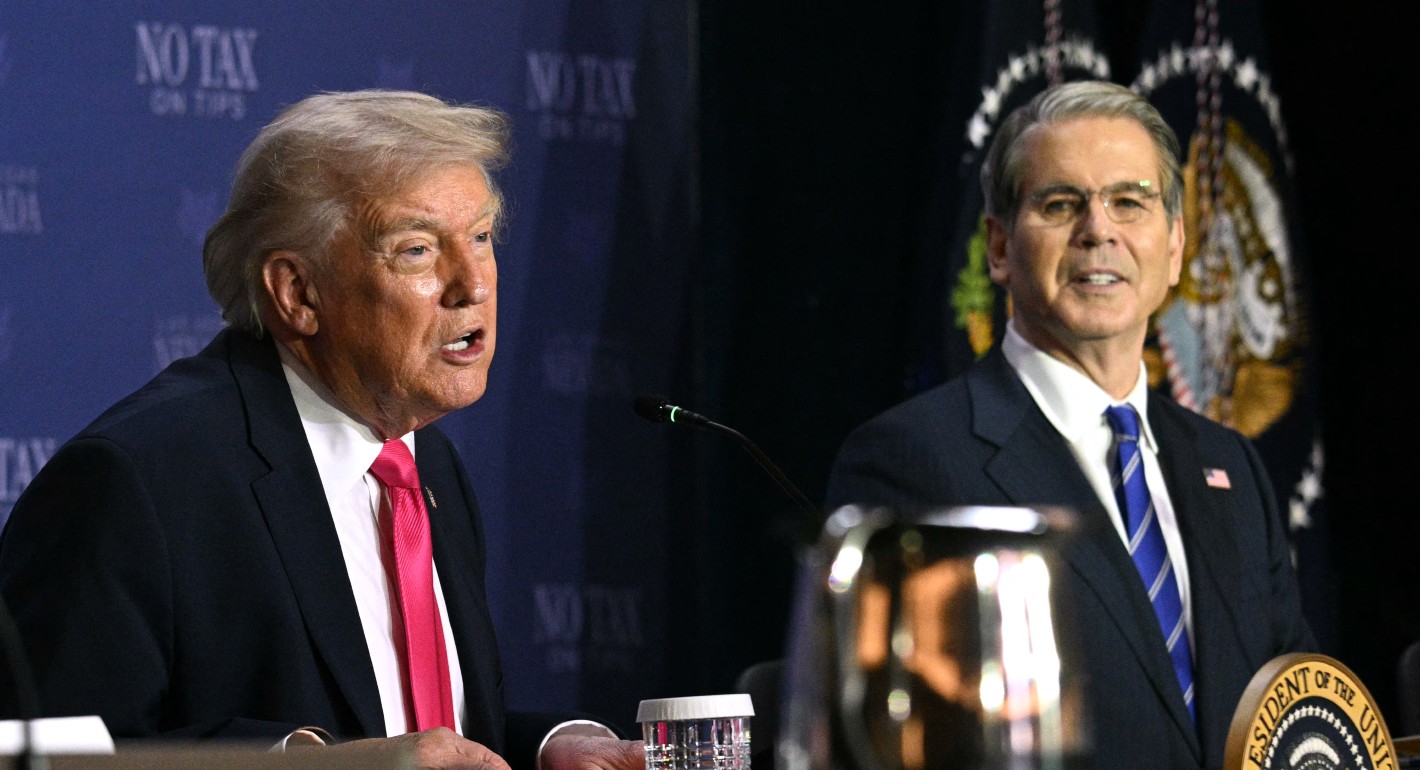
Source: Getty
Ukraine’s Allies Need a Better Framework to Assess Cyber Threats
Comparing the “most likely” and “most dangerous” scenarios can help navigate the uncharted Russian threat.
Russia’s invasion of Ukraine has once again forced Europeans to confront the threat of war brought about by an authoritarian’s warped version of history and fixation on securing an empire through military might. The echoes of centuries of conflict are all too familiar, but this crisis is unfolding in a world that is more interconnected than at any point in history. The advent of cyber power has added a novel dimension to the interactions between states and raises the specter that Russia could inflict harm directly against any country that opposes its invasion of Ukraine, without the risks and costs associated with physical force.
The question of what a hostile state can achieve through cyber operations is no longer a theoretical challenge for scholars and policymakers—it is an immediate risk-management problem for organizations of all types in all the countries allied against Russia. As commentary proliferates on what Russia might do in cyberspace, it is important to apply a probabilistic perspective to different assessments of the risk and not be seduced by the false certainty of predictions.
Russia is one of the most advanced cyber powers in the world, and Ukraine has been the target of some of its most sophisticated, ambitious, and damaging cyber operations. Nevertheless, most expert commentary has sought to downplay fears that cyber attacks will have a decisive effect in Ukraine or be used to create catastrophic harm in countries opposing Russia. And the activity reported to date has not indicated large-scale or especially damaging cyber operations. The problem is that we are in uncharted territory, and risk management needs a firmer foundation than deciding whose prediction to believe. It needs a framework that accounts for the options available to Russia and the uncertainty that attaches to President Vladimir Putin’s decisions, promoting an assessment of the likelihood of different courses of action.
The most important approach is to recognize that most analyses bring a specific, and usually unacknowledged, perspective of the threat. When scholars examine how cyber power could serve Russian aims, they usually articulate the “most likely” course of events—one that can be defended empirically. Consequently, most (although not all) academic research suggests that cyber operations will take a supporting role to the use of physical force in Ukraine and are unlikely to serve as strategic tools of escalation or deterrence. These moves will focus on subversive aims such as disruption, espionage, and political influence. By contrast, news reports and security-focused analysis often focus on the “most dangerous” manifestations, such as the prospect of cyber war, both to grab attention and because there is refuge for the analyst in warning of the worst imaginable outcomes, such as the crippling of economies or global systemic impacts. A probabilistic approach begins from assessing the threat and risk under most likely and most dangerous conditions, with the aim of guaranteeing preparedness for the most likely scenarios and enabling the difficult decisions on what upper magnitude of risk can or should be mitigated.
Those trying to make sense of the warnings to protect their organizations could apply this framework to current reporting, analysis, observed trends, and the consensus view of scholars to create a set of operations that Russia is most likely to pursue. Against Ukraine, this includes targeted attacks against military forces to disrupt and, in some cases, degrade capabilities; continuous interference in Ukrainian infrastructure and key sectors of the economy, aiming to undermine the capacity to fight; and information operations to build and sustain domestic support and undermine the Ukrainian will.
To deter escalation and signal resolve against countries opposed to Russia’s war, the most likely options include malware-based cyber attacks, such as ransomware and wipers, together with distributed denial of service attacks, used to inflict moderate disruption and economic harm. The strategic aim of these attacks would be to demonstrate the threat while limiting the possibility of escalation to direct conflict. As a result, target sets would be broad (such as exploitation of common vulnerabilities and exposures), with a high possibility of cascading effects. This likely wouldn’t result in a lasting effect at the strategic level, but individual organizations could suffer severe economic damage. Finally, it could deploy information operations to create alternative narratives, undermine confidence in leaders’ decisions, and stoke domestic unrest.
These risks should form the baseline for more detailed investigations to assess specific threats, vulnerabilities, and exposures at the level of individual organizations.
Nevertheless, the high degree of uncertainty means that much more severe risks are plausible. One way of accounting for high-impact, low-probability occurrences is to formulate a “most dangerous” set of scenarios rooted in the assessment of current Russian capability and intent, together with theories of the possible impacts. Importantly, this scenario extends beyond observed trends to formulate actions in plausible yet severe circumstances.
Russia’s most dangerous plausible actions in support of military operations in Ukraine could include cyber operations that are used to identify targets for attacks or security operations against the general population; a limited number of cyber attacks against operational technology that could cause physical damage and small numbers of casualties, generating disproportionate fear owing to their novelty; and information operations that foment doubt and discontent sufficient to unseat the government in Kyiv.
Against countries opposed to the Ukraine war, the most dangerous plausible actions Russia could deploy include cyber attacks used to create systemic disruption through compromising strategic targets such as shared services, internet infrastructure, and critical sectors, as well as indiscriminate cyber attacks at a tempo and scale that create costs and disruption sufficient to undermine popular support for a strategy of opposition to Russia. Putin might also succeed in creating limited disruptions to critical infrastructure, which could generate widespread uncertainty, provoking panic-buying and civil unrest.
It is important to recognize that the “most dangerous” label does not amount to the worst imaginable events but is designed to form the upper limit of risk that an organization should be expected to prepare for. The aim is not to predict exactly what will unfold, but to represent the features and magnitude of plausible but severe Russian cyber operations.
Resilience to unprecedented threats requires a forward-looking view, and high-impact, highly uncertain risks involve difficult decisions about where to prioritize effort. Analysis that lays out every conceivable nightmare simply transfers the problem, doing nothing to assist those hard decisions. Transparency and rigor are vital to making this type of analysis useful, since its value will ultimately lay in decisionmakers’ confidence in accepting its judgments.
Putin has brought war to Europe. Cyber power is a novel dimension that adds to the potential for fear, uncertainty, and doubt. In rallying attention to this challenge, it is important to apply a probabilistic perspective to the multiplying predictions of what this new dimension means for risk management and the hard decisions ahead.
About the Author

Former Nonresident Scholar, Technology and International Affairs Program
Nick Beecroft was a nonresident scholar in the Technology and International Affairs Program at the Carnegie Endowment.
- What the Russian Invasion Reveals About the Future of Cyber WarfareQ&A
- Evaluating the International Support to Ukrainian Cyber DefenseArticle
Nick Beecroft
Recent Work
Carnegie does not take institutional positions on public policy issues; the views represented herein are those of the author(s) and do not necessarily reflect the views of Carnegie, its staff, or its trustees.
More Work from Carnegie Endowment for International Peace
- Trump’s AI Order Won’t Stymie U.S. Competition with ChinaCommentary
Beijing regulated AI—and then Chinese AI companies took off.
Matt Sheehan
- Are Data Centers the Villains in the Battle Over Electricity?Commentary
Examples from Virginia and Lake Tahoe reveal complex situations that governments could use to fund critical grid upgrades.
Kate Gordon, Noah Gordon
- In the Middle East, Europeans Bow Down to the United StatesCommentary
Europe seems to have accepted its sidelining in the Middle East. The EU must reassert its support for the international rules-based order and step up engagement.
Rym Momtaz
- Beyond the Hype: Assessing Hyperscaler Nuclear Commitments Against U.S. Energy RealitiesPaper
The coming decade will require technology companies to decide how nuclear fits into their energy strategies—and grapple with the obligations that follow.
John Pendleton, Mackenzie Schuessler
- Is Belarus Really Set to Return to the Ukraine War?Commentary
By reminding the world that Lukashenko is a threat to NATO and Ukraine, Kyiv is trying to return the focus to why the Belarusian regime needs to be contained rather than rewarded.
Artyom Shraibman