Beijing’s AI diplomacy is pivoting from infrastructure and associated technical standards toward a more comprehensive effort aimed at recrafting global norms and institutions of AI governance.
Arindrajit Basu

Source: Getty
If U.S. policymakers continue down the path of restricting China’s access to frontier AI, they will eventually have to implement some sort of restriction on cloud access.
Since the first Donald Trump administration, the U.S. government has sought to restrict the ability of strategic competitors—most notably China—to produce advanced semiconductors. The concern is that such chips would accelerate competitors’ development of AI-driven military and surveillance capabilities. Yet while industry analysts and lawmakers debate the technicalities of physical chip controls, a largely unregulated channel—the cloud—is giving China access to computing power without the need to possess the chips themselves. In November 2025, the Wall Street Journal reported that INF Tech, a Shanghai-based start-up, has been remotely accessing around 2,300 leading-edge Blackwell chips through an Indonesian data center to train AI systems for financial and scientific applications. Also, Chinese tech giants Alibaba and ByteDance have been tapping into Nvidia chips housed in other Southeast Asian data centers to train their latest large language models.
These are not isolated cases. At least eleven state-linked Chinese entities have sought access to restricted U.S. technologies through cloud services in third-party countries, and last December, China’s Tencent struck a $1.2 billion deal with a Japanese cloud provider for access to 15,000 B200 chips. The Southeast Asian data center market alone is projected to exceed $30 billion by 2030, with U.S. hyperscalers investing more than $21 billion in AI infrastructure across Malaysia, Indonesia, and Thailand. Much of this compute will serve Chinese customers who have reserved it in five-to-seven-year contracts. These rental arrangements are not clandestine or illicit: under current U.S. law, they are perfectly legal—even if the data centers are inside the United States.
At least eleven state-linked Chinese entities have sought access to restricted U.S. technologies through cloud services in third-party countries. Under U.S. law, they are perfectly legal.
U.S. policymakers have made periodic efforts to close this loophole. Joe Biden’s administration took some limited steps toward restricting cloud access through its AI Diffusion Rule, but the second Trump administration suspended it before it took effect.1 Congress has tried as well: the Remote Access Security Act of 2024 passed the House as part of a larger package of legislation aimed at addressing China and national security, but the legislation stalled in the Senate.
Now, a revised Remote Access Security Act (RASA) has cleared the House once again. The bill has bipartisan support and broad appeal among China hawks, but it faces pushback from industry groups and foreign governments wary of a sweeping new statutory authority over a transnational service. Ultimately, the viability of cloud controls will depend on the scope of remote access restrictions, the technical robustness of their enforcement, and the U.S. government’s ability to resolve the thorny definitional questions that arise when cloud services are treated as exports.
Cloud compute allows customers to rent the computing power of semiconductors over the internet from anywhere in the world, without needing physical access to the underlying chips. Its applications range from running video games and financial simulations to training advanced AI models. All told, customers spend hundreds of billions on cloud services worldwide, with AI accounting for a growing slice of that pie. While physical access to chips remains necessary for some applications, such as autonomous weapons systems or real-time battlefield decisionmaking, cloud compute is more than sufficient for training frontier models, conducting intelligence analysis, and meeting most commercial AI needs.
Two separate loopholes are at play: Chinese companies can legally lease compute either from third-country or U.S.-based clouds. As discussed earlier, there is solid evidence that Chinese firms exploit the third-country loophole. Chinese companies such as Alibaba and ByteDance seem to have primarily relied on remotely accessing Nvidia chips in Southeast Asia to train their most advanced models. China’s exploitation of the U.S.-based loophole is probably also happening, but information about this is much more limited. Most likely, Chinese companies prefer third-country compute because they know that Washington has more legal and practical ability to collect intelligence within U.S. borders.
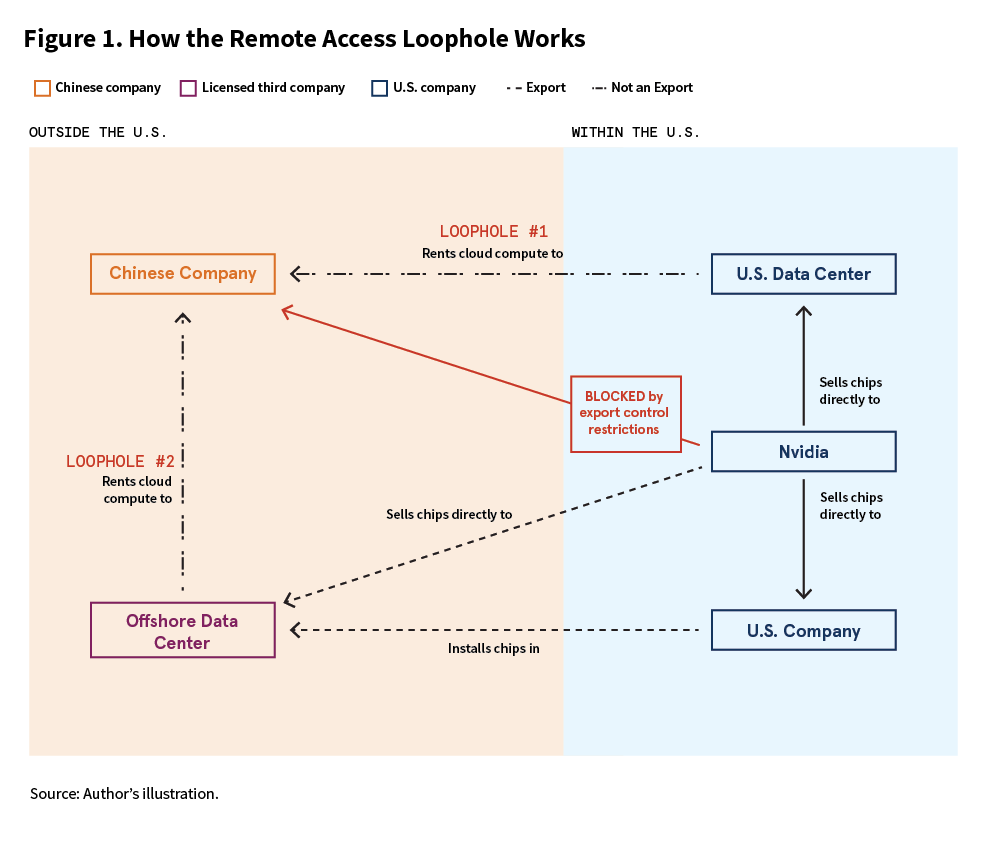
The U.S. government has taken few steps to close either loophole. The U.S. Bureau of Industry and Security (BIS) has the authority to restrict cloud compute offered by foreign data centers that use U.S. chips by imposing license conditions on chips exports. Yet this authority has not historically been exercised, likely reflecting a strategic calculation that remote access does not yet pose an imminent threat to national security. Meanwhile, for compute in U.S.-located data centers, BIS has limited tools to restrict remote access. Sales to U.S. companies operating in the United States, even subsidiaries of foreign parents, are not exports governed by BIS authorities.
The failure by Congress and the executive branch to close these loopholes suggests there may be a strategic purpose behind them. Leaving cloud access unregulated gives the U.S. government a window into the activities of Chinese tech companies, preserves market share for American innovation and cloud services, and maintains leverage for future U.S. action. Whether these benefits justify the security risks is the central question confronting policymakers—and the subject of intensifying debate in Congress.
RASA attempts to close both loopholes by redefining “exports” to include remote access to compute, thereby expanding the authority of export control regulations and subjecting cloud services to government restrictions. If BIS issues export control regulations under this new authority, cloud service providers would be required to verify that their buyers and end users were unrestricted or licensed entities. The bill would also grant BIS the authority to impose civil and criminal penalties on noncompliant companies, whether based abroad or operating within the United States.
Closing both loopholes at once makes sense. Restricting only rentals to foreign data centers would naturally encourage Chinese firms to consider pivoting toward the other loophole—renting cloud compute directly from U.S.-based data centers.
The core rationale for cloud controls is straightforward: it is logically inconsistent to restrict the sale of physical chips while allowing their computing power to be accessed remotely. Proponents argue that controlling access to high-end compute is, first and foremost, a national security imperative. AI systems are increasingly central to warfighting and intelligence operations, and any channel that provides adversaries with advanced compute poses a direct security risk. For instance, the compute accessed through the cloud relies on the same chips used by the Pentagon for projects working on automated targeting. Mike Lawler, the sponsor of RASA, has described cloud rentals as the “weakest link” in the U.S. export control regime. The House Select Committee on the Chinese Communist Party has echoed this assessment, warning that Chinese-aligned entities are exploiting these gaps to access sensitive U.S. technologies.
The core rationale for cloud controls is straightforward: it is logically inconsistent to restrict the sale of physical chips while allowing their computing power to be accessed remotely.
Cloud controls could also strengthen the United States’ diplomatic hand. The Trump administration has drawn significant bargaining leverage from its power to approve or deny export licenses, securing continued access to Chinese rare earth minerals in part in exchange for suspending newly expanded export control rules. But this leverage is waning. Beijing has required Chinese tech companies to increasingly adopt homegrown chips, and its response to the Trump administration’s willingness to export Nvidia H200 processors has been lukewarm. China is reportedly considering its own restrictions on chip imports. The unfettered ability to access frontier-level chips remotely provides yet another reason why Beijing feels less dependent on physical chips from the United States.
Blocking remote access to frontier compute would also make conditional chip licensing a more potent bargaining tool. By eliminating alternative sources of high-end compute, the United States gains more leverage—specifically regarding chips that are slightly more powerful than China’s best domestic versions. Even RASA’s authority alone could serve as a lever for threatening cloud compute restrictions and securing policy concessions without mandating that BIS do anything concrete.
Proponents of cloud controls also argue that allowing remote access threatens the commercial position of U.S. AI model developers, potentially undercutting the billions of dollars American companies have invested in the proprietary technology and intellectual property required to train frontier models. Nvidia contends that broad access to American compute locks foreign developers into the U.S. ecosystem, but advocates of cloud controls see it differently: Rather than securing loyalty, remote access gives Chinese competitors the runway to close the innovation gap. If Chinese AI companies can use U.S. computing power to match U.S. frontier models sooner, and potentially at lower cost, they could capture significant global market share. Proponents argue that restricting cloud access would meaningfully slow China’s AI development and help preserve U.S. commercial and national security advantages.
While controlling remote access to compute may seem like a natural extension of current national security protections, the case is more complicated than it appears.
During the Biden administration, BIS chose not to issue specific, enforceable licensing requirements for the remote use of advanced chips, despite having the theoretical authority to attach such conditions to physical chip exports. The Trump administration has continued that approach, and its overall export control policy has signaled a strategic pivot toward AI export promotion in an effort to hook China and other foreign buyers into the U.S. tech stack.
There is a logic to this restraint: Cloud controls represent a tool that could be deployed rapidly to curtail China’s AI capacity if its development becomes more threatening, but the administration can pull this lever only once. Use it too early, and the United States risks ceding future leverage for marginal near-term gains. Cloud controls, like previous export controls, could also prompt Beijing to further accelerate its push to fully indigenize semiconductor production and decouple from the U.S. ecosystem.
Cloud controls represent a tool that could be deployed rapidly to curtail China’s AI capacity if its development becomes more threatening, but the administration can pull this lever only once.
Restrictions on cloud access would also invite retaliation. When the United States expanded its export controls in 2025 to cover Chinese majority-owned subsidiaries, China’s Ministry of Commerce hit back by imposing sweeping export restrictions on rare earths (a move also prompted in part by hefty U.S. tariffs on Chinese goods). The two sides walked back these measures in a one-year truce, but this suspension was a tactical pause, not a policy shift. China retains significant leverage over critical supply chains—for example, it controls 93 percent of global magnet manufacturing, a crucial input for the U.S. defense sector—and can reassert it at any moment.
Another argument is that while the Southeast Asian cloud rental market seems like a substantial issue in aggregate, the scale of the remote access problem for individual renters remains in question. INF Tech remotely accessed 2,300 Blackwell chips—enough to fine tune frontier AI models, but orders of magnitude fewer than it would need to train new ones.
Some analysts also contend that cloud restrictions risk pushing users in third-party countries toward China’s competing AI stack. Remote access rules would need to depend on effective know-your-customer requirements. But assessments by the United States’ Government Accountability Office reveal that BIS is already stretched thin with ensuring hardware export compliance alone. In practice, the burden of vetting end users would fall largely on cloud service providers themselves, driving up costs and reducing revenue. Such a drag may push foreign-owned data centers to decrease their dependence on U.S. chips in favor of more convenient Chinese alternatives.
At first glance, this possibility might not seem so dire. Third-country data centers represent a smaller share of global buildout than their U.S. counterparts, and Chinese providers currently face a severe near-term shortage of domestic AI chips available for export. Nonetheless, the United States should be careful when invoking its chip supremacy to impose compliance demands. The Southeast Asian co-location market, where facilities lease physical space, power, and cooling for third-party servers, is expected to grow 42 percent faster than the rest of the world over the next five to seven years. If Southeast Asian countries turn away from U.S. chips, they might also spurn U.S. technical standards and data governance norms—a choice that could ripple across the region’s digital ecosystem.
Allowing Chinese entities continued access to U.S. cloud services may also benefit the U.S. intelligence community. Cloud providers generally say they do not monitor their users’ workloads, in part to protect customer privacy, but they have the technical capability to do so. The Foreign Intelligence Surveillance Act gives the U.S. government the authority to collect intelligence information from U.S. cloud providers on foreigners outside the United States. Cloud access thus provides a channel through which U.S. intelligence agencies might be able to gain visibility into the advancements and capabilities of Chinese AI developers. How valuable this intelligence is—and whether it outweighs the security costs of maintaining Chinese cloud access—remains an open question. But it is one that congressional lawmakers should evaluate before closing the door.
Finally, cloud controls will face diplomatic objections from third-party countries. Imposing know-your-customer requirements and end-use restrictions on foreign data centers will cost those countries revenue and relationships and will deepen U.S. extraterritorial authority over infrastructure on other nations’ soil. The Biden administration drew sharp reactions from adversaries and allies alike with its chip export controls; any expansion into cloud access will worsen those frictions, particularly with Southeast Asian nations that host some of the data centers in question. As Chinese alternatives to U.S. compute emerge, policymakers will need to weigh the net security benefits of cloud controls against the diplomatic costs of unilaterally extending U.S. regulatory reach into an inherently transnational service.
Beyond the policy pros and cons, the success of any cloud controls will also depend on a set of unresolved implementation questions. RASA and other similar proposals involve a straightforward conceptual move: They collapse the distinction between the physical movement of a chip and the remote utilization of its compute, treating intangible access as equivalent to physical shipments. But making this work in practice is another matter entirely.
The first question is scope. Would cloud controls impose restrictions on all foreign entities or just Chinese renters? If the answer is discretely Chinese renters, compliance officials or cloud services providers must shoulder the know-your-customer burdens inherent in trying to distinguish renter identities; foreign actors can distribute frontier training workloads across multiple data center clusters to obscure their total compute footprint, anonymous shell companies can obfuscate beneficial ownership, and virtual private networks can mask IP addresses. If the answer is instead to bar cloud access from all foreign entities, policymakers will have to contend with the significant lost revenue, industry discontent, and diplomatic friction that will result from cutting off all non-American access to cloud services.
A related question is how to define a restricted entity. Chinese firms on the Entity List and their majority-owned subsidiaries would presumably be restricted automatically.2 But to avoid the financial, industry, and diplomatic fallouts outlined above, policymakers may not want restrictions to cover foreign companies using U.S. cloud services for non-AI commercial purposes (for example, content streaming, enterprise storage, and cloud-based Software as a Service). Cloud controls that turn on the content of the activity in addition to the volume of computing power would therefore put the onus on service providers to distinguish between low-risk commercial use and high-risk training runs. This compliance measure could take on several forms, including restricting cloud access to chips that are barred from export, such as graphics processing units that exceed the computing abilities required for streaming, storage, and other regular services.
As with any regulation seeking to limit technology central to U.S.-China competition, cloud controls must reconcile security concerns with the costs of regulating a transnational service.
As with any regulation seeking to limit technology central to U.S.-China competition, cloud controls must reconcile legitimate security concerns with the practical and strategic costs of regulating a transnational service. Premature or overbroad application could do more harm than good—but so could inaction. Any successful implementation will need to be practically manageable to execute. One action immediately following the enactment of cloud controls would be to apply the strict know-your-customer mandates to known Entity List actors or affiliates and trigger such compliance audits when a renter exceeds a certain compute threshold. In addition, BIS could scrutinize licensing applications only for cloud clusters that exceed the aggregate compute necessary for training frontier-scale models.
If policymakers continue down the path of restricting China’s access to frontier AI, they will eventually have to implement some sort of restriction on cloud access, especially as AI becomes more advanced and integrated into military and intelligence applications. Getting this right will involve not only if or when questions, but also how, who, and what questions. Whatever the answers may be, Washington will play an important role in determining the future of U.S.-China AI competition.
James C. Gaither Junior Fellow, Technology and International Affairs Program
Noah Tan is a James C. Gaither Junior Fellow in the Carnegie Technology and International Affairs Program.
Carnegie does not take institutional positions on public policy issues; the views represented herein are those of the author(s) and do not necessarily reflect the views of Carnegie, its staff, or its trustees.
Beijing’s AI diplomacy is pivoting from infrastructure and associated technical standards toward a more comprehensive effort aimed at recrafting global norms and institutions of AI governance.

Arindrajit Basu
The full list of humiliations Europe has endured since Donald Trump returned to the White House makes for grim reading. But Washington’s adversarial approach to its allies undermines its own power base.

Rym Momtaz
Democratic institutions currently lack the capacity needed to govern AI-augmented deliberation in ways that serve democratic imperatives.

Micah Weinberg
The party’s domestic and regional roles have changed, so Lebanon should devise a disarmament strategy that encompasses this.

Michael Young
“Central Asia” as an analytical category is itself part of the problem. The term is a Soviet administrative inheritance, drawn along lines that served the convenience of Moscow. The Central Asian states the Soviets named no longer see themselves through this category alone and are not aligning across political blocs but are instead building external partnerships sector by sector, assigning different partners to different functions.

Jennifer B. Murtazashvili