Power assessments shape our perceptions of the limits of the possible, but quantitative rankings and dashboards can provide false confidence.
Nicholas Kitchen
{
"authors": [
"Tim Maurer"
],
"type": "other",
"centerAffiliationAll": "dc",
"centers": [
"Carnegie Endowment for International Peace"
],
"collections": [
"Cyber and Digital Policy"
],
"englishNewsletterAll": "ctw",
"nonEnglishNewsletterAll": "",
"primaryCenter": "Carnegie Endowment for International Peace",
"programAffiliation": "NPP",
"programs": [
"Nuclear Policy",
"Technology and International Affairs"
],
"projects": [],
"regions": [
"Iran"
],
"topics": [
"Foreign Policy",
"Technology"
]
}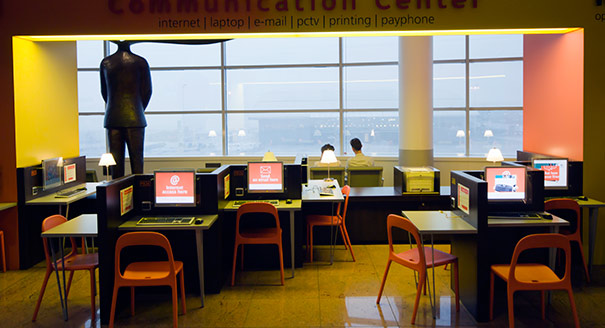
Source: Getty
States use proxies to project power through cyberspace, some capable of causing significant harm. But there is a lack of clarity on what, exactly, the term ‘proxy’ means.
Source: Journal of Conflict and Security Law
States use proxies to project power through cyberspace, some capable of causing significant harm. In recent years, media outlets have published reports about proxies using Information and Communications Technologies (ICTs) from Northeast Asia to India, Pakistan, the Middle East, and Eastern Europe. Two of the landmark documents providing insight into how the international community thinks about rules of the road for cyberspace explicitly reference the term ‘proxies’. However, neither report defines ‘proxy’, nor does the term easily translate into non-English languages. This article therefore reviews what this term means and how it has been used in various contexts. It focuses on the subset of proxies that are non-state actors used by a state actor, analysing the different logical distinctions and levels of detachment between a state and a non-state actor’s activity. The goal is 2-fold: first, to provide a framework to think about the diverse array of existing proxy definitions; second, to conceptualise the relationships between a state and non-state proxies that can offer a guide for political decision-makers and a roadmap for future research on proxy actors and cyberspace.
This article was originally published in the Journal of Conflict and Security Law.

Tim Maurer
Former Senior Fellow, Technology and International Affairs Program
Dr. Tim Maurer was a senior fellow in Carnegie’s Technology and International Affairs program.
Carnegie does not take institutional positions on public policy issues; the views represented herein are those of the author(s) and do not necessarily reflect the views of Carnegie, its staff, or its trustees.
Power assessments shape our perceptions of the limits of the possible, but quantitative rankings and dashboards can provide false confidence.
Nicholas Kitchen
The debate over AI and work too often centers on displacement. Facing aging populations and shrinking workforces, East Asian policymakers view AI not as a threat, but as a cross-sectoral workforce strategy.

Darcie Draudt-Véjares, Sophie Zhuang
In its version of an AI middle power strategy, Seoul is pursuing alignment with the United States not as an endpoint but as a strategy to build industrial and geopolitical leverage. Whether this balance holds remains an open question.


Darcie Draudt-Véjares, Seungjoo Lee
This collection of essays by scholars from Carnegie India’s Technology and Society program traces the evolution of the AI summit series and examines India’s framing around the three sutras of people, planet, and progress. Scholars have catalogued and assessed the concrete deliverables that emerged and assessed what the precedent of a Global South country hosting means for the future of the multilateral conversation.



Nidhi Singh, Tejas Bharadwaj, Shruti Mittal, …
If Washington cannot adapt to the ongoing transformations of a multipolar world, its superiority will become a liability.

Amr Hamzawy